Cyber threats, including malware, phishing, and ransomware, are among the most severe threats to businesses today. For example, Google has found 100,000 malicious websites and 10,000 malicious files daily and has registered more than 2 million phishing sites, more than a 27% increase, in the past 12 months.
Small companies are often the targets of cyber threats because they are less likely to have strong security measures in place and don’t have a security team to protect themselves. As these threats grow, so does the demand for Information Security specialists, making this a very interesting career choice.
How To Become an Independent Information Security Consultant
The road to becoming an independent information security consultant often begins with an obsessive interest in information technology and computer science as a whole. Most already have a degree or experience in IT and then build up their knowledge through the many resources available, but none of these are prerequisites if you are really determined.
The only thing you need to do is get started, and be curious. Here some guidelines on where to get started
- Read books on security to get into the mindset of a professional
- Regularly listen to podcasts on security
- Take some (free) online cyber security and coding courses
- Try to understand existing and new vulnerabilities by following publications and news
- The Hacker News
- Latest cybersecurity vulnerability news
- Exploit Database - Exploits for Penetration Testers, Researchers, and Ethical Hackers
- CVS : Security vulnerabilities
-
CVE (mitre.org)
- CSO | Security news, features and analysis about prevention, protection and business innovation.
- Troy Hunt blog
- Daniel Miessler blog
- Online security challenges & environments to test/learn your skills
- Hack The Box: Hacking Training For The Best
- Proving Grounds: Virtual Pentesting Labs | Offensive Security (offensive-security.com)
-
Vulnerable By Design ~ VulnHub
- PentesterLab: Learn Web Penetration Testing
- Virtual Hacking Labs | Penetration Testing Training Labs & Courses
- Hacking-Lab Cyber Range
- OverTheWire: Wargames
-
HackThisSite
- Learn about well known security and privacy framework/standards to understand how you can get organized to protect companies
- Get an industry recognised security certification
- And many more publicly available resources & tools
- sbilly/awesome-security: A collection of awesome software, libraries, documents, books, resources and cools stuffs about security. (github.com)
- toniblyx/my-arsenal-of-aws-security-tools: List of open source tools for AWS security: defensive, offensive, auditing, DFIR, etc. (github.com)
-
zbetcheckin/Security_list: Great security list for fun and profit (github.com)
This list might look daunting at first, but reality is that the more you discover, the more it will spark your interest and the more you will learn. If you want to become a successful Cyber security professional, you are signing up for a life long learning path, with every day being filled with mind boggling new discoveries of technologies and techniques you did not know before.
Even if you start from scratch, and spend every day 30 minutes on any of the topics above, you'll be well set for a start in a security career one year from now
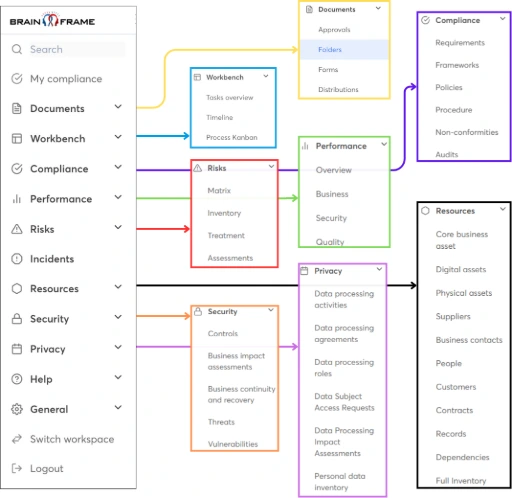
Once you are ready to go, don't forget to come back here, and look at how Brainframe will give you the wings you deserve in your security and compliance career
Good luck!

Start for free now!
Like with GDPR, don't wait until the last moment because this will only be more expensive and put unneeded stress on your teams!
Subscribe to our newsletter
By providing your email we'll send you updates on our service per email
(not more than one mail per week).